A technological breakthrough on the same scale as MPLS in the early 2000s, SD-WAN is at the heart of infrastructure transformation. LUCERNYS offers a summary of the SD-WAN and the relevant criteria to validate this choice.
SD-WAN technology
SD-WAN technology – acronym for Software-Defined Wide Area Network – allows aggregations of N links, from N operators, with N different technologies. This assembly brings throughput, resilience, economy and performance to the network. The solution also includes security features.
On top of the physical networks, a software network creates its own network through SD-WAN boxes in overlay mode, i.e. by mounting tunnels on top of the physical networks.
The architecture
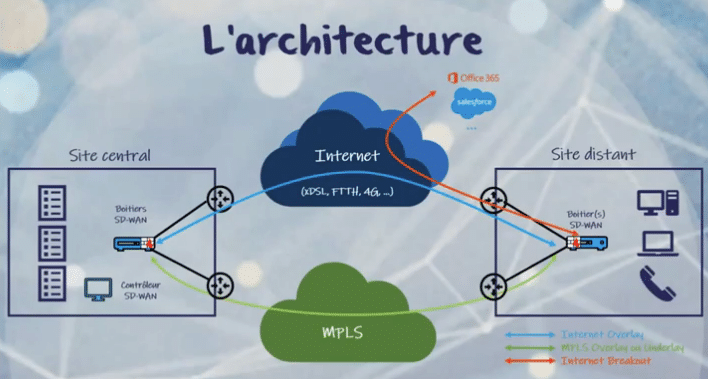
A remote site connected to a central site by N physical networks and N Internet networks.
A remote site is connected to a central site by N physical networks and N Internet networks via SD-WAN appliances. The boxes communicate by setting up tunnels over MPLS, over the Internet or to the Internet. The principle: this logical virtual network, built on top of physical networks, allows sites to communicate without the constraints of operators.
Why choose SD-WAN?
LUCERNYS has identified 7 criteria to identify if this technology is suitable for a given configuration and to help in the decision.
|
THE 7 KEY SD-WAN CRITERIA Throughput ° Cloud ° Security ° Resilience Performance ° Agility ° Cost |
- Flow rate
The SD-WAN allows to mix N networks, an answer adapted to the cloud component which justifies to take this technological orientation. Multiple links, carriers and technologies on a site-based SD-WAN box greatly limits connection problems. Throughput is also enhanced because the N links generated increase the bandwidth, and therefore the throughput.
- Cloud
The massive growth of the cloud calls for a stable, reliable and secure network solution to keep cloud-hosted applications running.
- Resilience and performance
With multiple networks and paths available, and with intelligent performance-based routing, SD-WAN provides stability of operation despite any outages, incidents, hacks or spikes in activity that may occur. Resiliency represents the ability of the network to operate despite network outages. Resilience is made possible by the multiplicity of technology linkages.
- Security
Security criteria can be very advanced with SD-WAN. Security is respected and stabilized through SD-WAN encryption. Security is inherently unchanged from a traditional MPLS solution.
Like MPLS, SD-WAN guarantees security with a central box and on-site boxes. Data travels through secure VPN tunnels between the site and the central site. Indeed, a VPN tunnel encrypts the data and makes it impossible to read. The SD-WAN appliance provides a default level of embedded security, which allows communication between two sites without risking data compromise.
- Agility
SD-WAN brings agility, especially in terms of operations, thanks to central controllers that enable routing intelligence in an easy way.
With the aggregation of N links on an SD-WAN box, the enterprise is no longer dependent on link delivery time, as with MPLS, or on a third party. The speed of deployment of the technology – in any area – is also a major advantage. With this technology, it doesn’t matter what the link is, it just has to exist.
- Costs
An MPLS link is expensive for companies. Companies with large networks, such as franchises, can now subscribe to the general public offers, often dividing the cumulative price of subscriptions by 3. SD-WAN also offers the possibility to multiply the links with different operators.
SD-WAN is best suited for enterprises with multiple locations. It is less suitable for companies that have a few locations with many employees that need highly capable networks. In this case, the gains are less important.
The costs directly related to SD-WAN are twofold:the cost of the SD-WAN boxes, which depends on their power, and the costs of deploying them to all sites.
SD-WAN features
SD-WAN is at the convergence of 3 worlds: the world of routing, the world of application QoS and the world of security.
- The world of routing.
SD-WAN offers key benefits from a routing perspective:
An “intelligent” performance-based routing solution.
Decisions can be made based on the quality of the underlying links. Thus, switching to an MPLS link can be done if the Internet link deteriorates. This notion of switching is very different from a traditional network.
The possibility to mix overlay and underlay.
With the overlay, we build tunnels, completely freeing ourselves from the notion of the underlying physics. However, building tunnels can be resource intensive. To avoid this, it is possible to choose the underlay option, especially on the MPLS brick, without setting up tunnels.
The possibility of aggregating separate links.
It is now possible to build sections that go far beyond the size of the physical links, which was not possible in a traditional network. Indeed, before the emergence of SD-WAN, you could not aggregate an MPLS link with an Internet link.
Local breakout,
This application offers the possibility to access directly to Salesforce, Office365, Amazon, Azure for example.
- The world of security.
The SSD-WAN (Secured SD-WAN) integrates an internal and external security brick. It guarantees to secure local flows (level 3 or 4), and UTM functionalities for external security (up to level 7) with URL filtering, application control, IDS / IPS, etc.
- The world of application QoS, or flow management.
Application QoS (Quality of Service) allows to prioritize a selection of links – for example voice or video – over other flows. The flow regulation, which is its main asset, can be adjusted in real time.
Application control provides the ability to prioritize incoming flows.
SD-WAN brings a central configuration, with a central controller that has local intelligence. So, if the controller goes down, SD-WAN appliances have the embedded intelligence to overcome that failure.
| LUCERNYS accompanies its customers towards SD-WAN, with an evaluation of the situation and needs. Then LUCERNYS identifies the most relevant solution and operator with the company’s configuration.
The choice of the SD-WAN player should be based on the criteria deemed most important for a given strategy. First and foremost, the ability to execute must be considered. |